
This project explores foundational techniques in information security, focusing on classic ciphers and cryptographic methods. It includes practical demonstrations of encryption and decryption techniques such as Caesar Cipher, Vigenère Cipher, Playfair Cipher, Transposition Ciphers, and modern approaches like the One-Time Pad and Affine Cipher. The aim is to understand the strengths and vulnerabilities of these methods and highlight their role in the evolution of cryptography. Interactive modules and visualizations help users grasp concepts like substitution, transposition, and brute-force attacks, making it both educational and engaging.
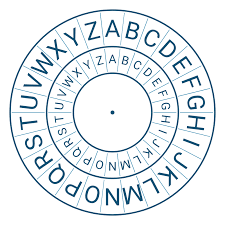
The Caesar Cipher is a substitution cipher that shifts the letters of the plaintext by a fixed number. It is one of the simplest and most widely known encryption techniques.
Brute Force Search systematically tries all possible keys to decrypt a message. It is a fundamental method to test the security strength of cryptographic systems.

The Playfair Cipher encrypts digraphs (pairs of letters) instead of single letters, using a 5x5 matrix to generate ciphertext. It offers better security than monoalphabetic ciphers.
The Vigenère Cipher is a polyalphabetic substitution cipher that uses a repeating keyword to encrypt plaintext, making frequency analysis attacks more difficult.

The One-Time Pad uses a random key that is as long as the plaintext. It is theoretically unbreakable if the key is truly random and used only once.
The Transposition Cipher rearranges the letters of the plaintext according to a specific system, preserving all original characters in the ciphertext.
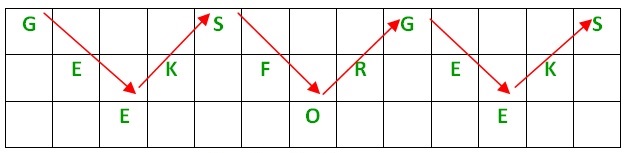
The Rail Fence Cipher is a transposition cipher that writes plaintext letters in a zigzag pattern across multiple rows and reads them row by row to form ciphertext.

The Affine Cipher is a monoalphabetic substitution cipher that combines multiplication and addition operations to encrypt each character in the plaintext.

Cryptography plays a vital role in securing online banking transactions. Techniques like SSL/TLS encryption ensure that sensitive data, such as login credentials and transaction details, are securely transmitted between customers and banks. With cryptographic algorithms like RSA and AES, data is encrypted and protected from potential eavesdroppers, preventing fraud and ensuring the safety of financial transactions.

With the growing concern over privacy, email encryption is essential for securing personal communications. PGP (Pretty Good Privacy) and S/MIME are two widely used protocols for encrypting emails, ensuring that only the intended recipient can read the message. These methods use asymmetric cryptography, where public and private keys protect the confidentiality of email content.

Blockchain technology relies heavily on cryptographic techniques like hashing and digital signatures to secure and verify transactions. Cryptocurrencies like Bitcoin use ECDSA (Elliptic Curve Digital Signature Algorithm) to authenticate transactions and ensure the integrity of the blockchain. Cryptography ensures that transactions are immutable and protected from tampering, enabling secure peer-to-peer transfers without a trusted intermediary.
Governments around the world use digital signatures for securely verifying official documents and communications. Digital signatures use public-key cryptography to authenticate the sender's identity and ensure the document's integrity. This technology is essential in fields such as tax filing, legal contracts, and government correspondence, where authenticity and non-repudiation are crucial.

With the rise of privacy concerns, secure messaging applications like WhatsApp and Signal use end-to-end encryption to ensure that only the sender and recipient can read the messages. These apps use a combination of symmetric and asymmetric encryption techniques, ensuring that messages are encrypted before they leave the sender's device and can only be decrypted by the intended recipient's private key.

Digital certificates are used to verify the authenticity of websites and enable secure communication over the internet. The HTTPS protocol uses SSL/TLS encryption, along with digital certificates, to ensure the confidentiality and integrity of data transmitted between the user’s browser and the server. This is essential for securing e-commerce transactions and protecting user privacy.